Many people are asking “How Does Carding Work?” While some are looking for a way to bypass OTP and withdraw cash from debit/credit cards, so here is an article that will put you through.
To save you from the long paragraphs of article, we recommend you contact us right away and ask your direct question, otherwise kindly read carefully.
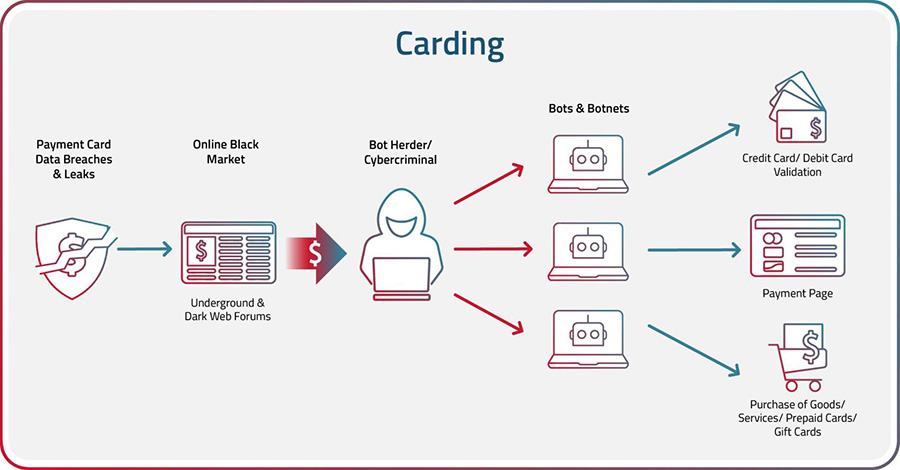
The process of executing a carding attack typically involves several steps:
- Obtain Credit/Debit Card Information: Carders obtain credit card information by stealing physical credit cards, purchasing credit card data on the dark web, or using techniques such as phishing, skimming, or malware to steal credit card information. Account Takeover (ATO) of user accounts on e-commerce or financial websites carried out by bots is yet another way for bad actors to steal payment card data.
- Validate Card Data: After carders obtain payment card data, they often use bots to validate the cards and check the balances or credit limits on the card with credential stuffing and credential cracking. Credential stuffing is a technique that uses bots to rapidly enter lists of breached or stolen card data to try to validate them. Credential cracking is the process of entering random characters over multiple attempts in the hope of eventually guessing the right combination.
- Drop Shipping: A drop is a location where the fraudster can have fraudulently purchased items shipped without revealing their own identity or location.
- Make the Purchase: The cybercriminal can use the stolen credit card information to make purchases online or in-store. They may use a technique known as “card present” fraud to create a counterfeit card and make purchases in-person. “Card not present” fraud indicates when the purchase was made online.
- Keep or Resell the Goods: Once fraudsters receive the fraudulently purchased items, they will either keep them for personal use or resell them on the black market for cash.
Infographic Stages of Carding
What are the Most Common Carding Attacks?
Phishing: Cybercriminals send a fake email or text message to the victim, posing as a legitimate company. They request that the victim provides their credit/debit card information, which they can use to make fraudulent purchases.
Social Engineering: The fraudster poses as a legitimate representative of a company or financial institution and convinces the victim to provide their credit card information over the phone or through email.
Identity Theft: A thief steals a victim’s personal information, such as their name, address and social security number, and uses that information to open new credit card accounts or make purchases using the victim’s existing credit card.
Malware: Nefarious actors install malicious software on a computer or mobile device to capture the victim’s payment card information when they make online purchases.
Card Skimming: In this type of fraud, criminals use a device known as a skimmer to steal credit card information. The skimmer is placed on a legitimate card reader, such as an ATM or gas pump, and records the card data when the victim swipes or inserts their card.
Already Have The Card Details And Want To Withdraw Money From The Debit/Credit Card Bypassing OTP?
Why going through all the stress outlined on above paragraphs?
Here Is The Real “Advanced Carding” The Solution solution!
Asking “How Does Carding Work?” Is irrelevant because this is a direct guide on how to withdraw money from debit card and convert it to cryptocurrency without trace. Learn more here, for more information contact us right away.